TRANSACTION MANAGEMENT AND CONCURRENCY CONTROL | Database Transactions Through Query Optimization and Security Best Practices | Realcode4you
- realcode4you
- 11 hours ago
- 13 min read
Database transactions form the backbone of reliable data management in modern applications. They ensure data integrity, consistency, and durability even in complex, multi-user environments. Yet, many systems struggle with slow transaction processing and vulnerabilities that expose sensitive data. Improving database transactions requires a clear focus on two critical areas: query optimization and security best practices. This post explores practical strategies to enhance transaction performance while safeguarding data.

Database servers handling multiple transactions simultaneously in a data center environment
Understanding Database Transactions and Their Importance
A database transaction is a sequence of operations performed as a single logical unit of work. Transactions follow the ACID properties:
Atomicity: All operations succeed or none do.
Consistency: Transactions bring the database from one valid state to another.
Isolation: Concurrent transactions do not interfere with each other.
Durability: Once committed, changes persist even after failures.
These properties ensure that data remains accurate and reliable. For example, in banking, transferring money between accounts involves debiting one account and crediting another. Both steps must complete together or not at all to avoid errors.
Poorly managed transactions can lead to data corruption, deadlocks, or performance bottlenecks. Optimizing queries and securing transactions helps maintain system responsiveness and trustworthiness.
How Query Optimization Improves Transaction Performance
Query optimization focuses on making database queries run faster and use fewer resources. Since transactions often involve multiple queries, optimizing them reduces overall transaction time and resource consumption.
Key Techniques for Query Optimization
Indexing
Creating indexes on columns frequently used in WHERE clauses or JOIN conditions speeds up data retrieval. For example, indexing a customer ID column can reduce search time from seconds to milliseconds.
Avoiding SELECT *
Selecting only necessary columns reduces data transfer and processing. Instead of `SELECT * FROM orders`, use `SELECT order_id, order_date FROM orders`.
Using Query Execution Plans
Most database systems provide execution plans that show how queries run internally. Analyzing these plans helps identify slow operations like full table scans or inefficient joins.
Limiting Joins and Subqueries
Complex joins and nested subqueries can slow queries. Simplifying queries or breaking them into smaller parts can improve speed.
Caching Frequent Queries
Storing results of common queries in cache reduces database load. For example, caching product lists that rarely change improves response times.
Example: Optimizing a Transaction Query
Consider a transaction that updates inventory after a sale:
```sql
BEGIN TRANSACTION;
UPDATE inventory SET quantity = quantity - 1 WHERE product_id = 123;
INSERT INTO sales (product_id, sale_date) VALUES (123, CURRENT_DATE);
COMMIT;
```
If the `inventory` table lacks an index on `product_id`, the update will scan the entire table, slowing the transaction. Adding an index on `product_id` speeds up the update, reducing transaction time.
Best Practices for Securing Database Transactions
Security is critical to protect data from unauthorized access, tampering, or loss. Transactions often involve sensitive information, making security a top priority.
Essential Security Measures
Use Parameterized Queries
Avoid SQL injection by using parameterized queries or prepared statements. This ensures user inputs are treated as data, not executable code.
Implement Role-Based Access Control (RBAC)
Limit database permissions based on user roles. For example, only allow read access to reporting users and full access to administrators.
Encrypt Sensitive Data
Use encryption for data at rest and in transit. Encrypting columns like passwords or credit card numbers protects data even if the database is compromised.
Enable Audit Logging
Track transaction activity to detect suspicious behavior or unauthorized changes. Logs help with compliance and forensic analysis.
Use Secure Connections
Enforce SSL/TLS for database connections to prevent data interception.
Example: Preventing SQL Injection in Transactions
Instead of building queries by concatenating strings:
```sql
sql = "UPDATE users SET password = '" + new_password + "' WHERE user_id = " + user_id;
```
Use parameterized queries:
```sql
sql = "UPDATE users SET password = ? WHERE user_id = ?";
execute(sql, [new_password, user_id]);
```
This approach blocks attackers from injecting malicious SQL code.
Combining Optimization and Security for Reliable Transactions
Optimizing queries and securing transactions are not separate tasks. They must work together to deliver fast, safe database operations.
Efficient queries reduce the window for attacks by minimizing transaction duration.
Secure transactions prevent data corruption that could arise from malicious interference.
Monitoring performance and security logs together helps identify anomalies that affect both speed and safety.
Tools and Technologies to Support Optimization and Security
Several tools can help developers and database administrators improve transactions:
Database Profilers and Analyzers
Tools like SQL Server Profiler, MySQL EXPLAIN, or PostgreSQL pg_stat_statements provide insights into query performance.
Security Scanners
Automated scanners detect vulnerabilities such as SQL injection risks or weak permissions.
Connection Pooling
Managing database connections efficiently reduces overhead and improves transaction throughput.
Encryption Libraries
Use libraries that integrate with databases to handle encryption transparently.
Practical Tips for Developers and DBAs
Regularly review and update indexes based on query patterns.
Test queries with realistic data volumes to identify bottlenecks.
Apply the principle of least privilege for database users.
Keep database software and patches up to date.
Use transaction isolation levels appropriate for your workload to balance consistency and concurrency.
Database transactions are vital for data integrity and application reliability. By focusing on query optimization, you can speed up transactions and reduce resource use. At the same time, applying security best practices protects data from threats and ensures compliance. Together, these approaches build a strong foundation for managing data effectively.
Sample Practice Assesment
Overview
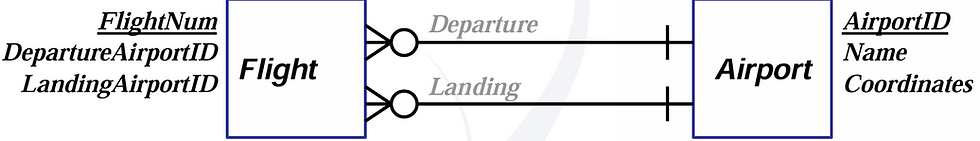
HueHub is a locally operated business in Aotearoa New Zealand that supplies a range of paint and related products. Figure 1 illustrates the Entity-Relationship Diagram (ERD) of HueHub's relational database, outlining the key entities along with its attributes and the relationships among the entities.
Note the following key features that are important for completing Tasks 1, 2, and 3:
A customer can make multiple purchases, and each purchase is recorded as a separate invoice in the INVOICE table. The date of each purchase is stored in the INV_DATE column.

An invoice contains one or more line items, which are recorded in the LINE table. Each line item represents a single product purchased and includes details such as quantity (LINE_QTY) and unit price (LINE_PRICE).
The total cost of all items in an invoice is stored in the INV_TOTAL column of the
INVOICE table.
Every invoice is associated with an employee who processed the sale via the
EMPLOYEE_ID column in the INVOICE table.
A customer's outstanding balance is tracked in the CUST_BALANCE column of the
CUSTOMER table. This balance increases with credit purchases.
The quantity on hand for a product is stored in PROD_QOH in the PRODUCT table. It decreases when products are sold and increases when stock is supplied by vendors.
A vendor may supply multiple products, and each product can be supplied by multiple vendors. However, each vendor can only supply each product once. This many-to-many relationship is captured in the SUPPLIES table, which associates each product (PROD_CODE from the PRODUCT table) with the vendor (VEND_ID from the VENDOR table) supplying it.
The two transactions described below, T1 and T2, must be executed and reflected in HueHub's database:
– Transaction T1
On 15 April 2025, customer 574 makes a credit purchase that includes two products.
10 units of product 1021-MTI at $62.GG per unit
10 units of product 2233-GJH at $23.2G per unit
This transaction is recorded under invoice number 12600 and the sale is processed by employee 8350G.
– Transaction T2
On 20 April 2025, vendor 22 supplies 50 units of product 1021-MTI for the first time.
Task 1: Implementing Transactions
Write SQL statements to implement the two transactions, T1 and T2. Use START TRANSACTION (or BEGIN) and COMMIT to group the SQL statements into logical units of work. Make sure that all affected tables are appropriately modified.
Task 2: Creating a Transaction Log
Manually create a transaction log that records the actions performed during the serial execution of Transactions T1 and T2, where T1 is fully completed before T2 begins. The log should be presented in a structured tabular format with the columns listed below:
TRL_ID: A unique identifier for each log entry
TRX_NUM: The transaction number (e.g., T1 or T2)
PREV_PTR: Pointer to the previous transaction log entry
NEXT_PTR: Pointer to the next transaction log entry
OPERATION: Type of action performed (e.g., START, INSERT, UPDATE, COMMIT)
TABLE: Name of the table affected
ROW_ID: Identifier for the affected row
ATTRIBUTE: Specific column that was modified
BEFORE_VALUE: Value prior to the operation
AFTER_VALUE: Value after the operation
Note: Before the execution of Transactions T1 and T2, the value of PROD_QOH for product 1021-MTI is 100, for product 2233-GJH is 200, and the value of CUST_BALANCE for customer 574 is 0. For other fields not explicitly provided, you may assume reasonable values if necessary.
Task 3: Handling Concurrent Transactions
a) Consider the concurrent execution of transactions T1 and T2 without any
concurrency control mechanisms in place.
Provide an example schedule where the interleaving of operations from transactions T1 and T2 results in a lost update problem. Explain how and why the lost update occurs. Include a table to support your explanation, illustrating the sequence of interleaved execution of the transactions. The table should have at least the following columns:
TIME: Logical sequence of operations
TRANSACTION: Transaction performing the operation (e.g., T1 or T2)
STEP: Specific operation being performed (e.g., Read, Write) with data element.
STORED VALUE: Data value read or written
b) Assume a concurrency control mechanism is in place, with transactions T1 and T2 serialised using the two-phase locking protocol (2PL) at the table-level granularity.
Create a chronological list of actions for transactions T1 and T2 to illustrate the correct sequence of operations. Indicate clearly when a transaction performs data manipulation (Read or Write), locking (Shared Lock or Exclusive Lock), unlocking, and specify the data element is being manipulated, locked or unlocked (e.g., table- level or row-level). Present your answer in the same table format as Task 3(a).
Explain how the two-phase locking protocol resolves the lost update problem identified in Task 3(a).
Task 4: Detecting and Handling Deadlocks
Given the schedule in Table 1, where T001, T002, T003, and T004 represent transactions, and READ(X) and WRITE(X) denote read and write operations on data items X1, X2, and X3, assume the following:
A shared lock is requested immediately before each READ(X) operation.
An exclusive lock is requested immediately before each WRITE(X) operation.
All locks must be released immediately after the commit of the respective transaction.
a) Update the schedule by adding lock and unlock requests.
For each lock request, indicate whether it is GRANTED or DENIED next to the request. If a lock is denied, indicate that the transaction must WAIT. Use the following notations to modify the schedule:
S-LOCK(X): Request a shared lock on data item X.
X-LOCK(X): Request an exclusive lock on data item X.
UNLOCK(X): Release the lock on data item X after the transaction commits.
b) Discuss whether the schedule results in any deadlocks. If a deadlock occurs, explain how it would be handled using both the Wait-Die and Wound-Wait schemes.
For each scheme, explain which transaction should wait and which one should be aborted or rescheduled, providing clear justification for each action. Describe how the deadlock would be resolved so that transactions can eventually proceed and complete.
Assume the timestamps for transactions T001, T002, T003, and T004 are 1, 2, 3, and 4, respectively.

Task 5: Recovering Transactions
Table 2 presents the transaction log records for three concurrent transactions (101, 102, and 103) that were executing at the time of a system crash.
The following are the relevant table structures involved in these transactions:
BOOK(BOOK_ID, TITLE, AUTHOR, GENRE, YEAR, STATUS, LOCATION)
LOAN(LOAN_ID, BOOK_ID, MEMBER_ID, ISSUE_DATE, RETURN_DATE)
Assume that the database recovery process uses either the write-through (immediate update) technique or the deferred-write (deferred update) technique to restore the system to a consistent state.
For each recovery technique, describe in detail how the system should handle recovery after the crash. Clearly identify which transactions need to be redone, which need to be undone, and which can be left unchanged. Use transaction and log entries to explain how these changes (if any) are implemented and justify the reasoning behind each decision.

PART B - DATABASE PERFORMANCE TUNING AND QUERY OPTIMISATION (25 POINTS)
Overview
The schema used to manage agricultural data for landowners overseeing crops in the Selwyn District is defined by the SQL script below:
CREATE TABLE LANDOWNER ( OWNER_ID INT, OWNER_FNAME VARCHAR(50), OWNER_LNAME VARCHAR(50),
OWNER_ADDRESS VARCHAR(150), OWNER_CONTACT VARCHAR(20), PRIMARY KEY (OWNER_ID)
);
CREATE TABLE LANDPARCEL ( PARCEL_ID INT,
OWNER_ID INT,
PARCEL_SIZE DECIMAL(5,2), PARCEL_LOCATION VARCHAR(150), PRIMARY KEY (PARCEL_ID),
FOREIGN KEY (OWNER_ID) REFERENCES LANDOWNER(OWNER_ID)
);
CREATE TABLE CROP ( CROP_ID INT,
CROP_NAME VARCHAR(50), VARIETY_NAME VARCHAR(50), CROP_SEASON VARCHAR(20), CROP_YIELD DECIMAL(5,2), PRIMARY KEY (CROP_ID)
);
CREATE TABLE LANDUSAGE ( USAGE_ID INT, PARCEL_ID INT,
CROP_ID INT, USAGE_START_DATE DATE, USAGE_END_DATE DATE, PRIMARY KEY (USAGE_ID),
FOREIGN KEY (PARCEL_ID) REFERENCES LANDPARCEL(PARCEL_ID), FOREIGN KEY (CROP_ID) REFERENCES CROP(CROP_ID)
);
Assume you are required to retrieve the names of landowners in the Selwyn District who grew "WHEAT" in the "SPRING" season on parcels larger than 50 hectares.
The following SQL query retrieves that information:
SELECT LANDOWNER.OWNER_FNAME, LANDOWNER.OWNER_LNAME FROM LANDOWNER
INNER JOIN LANDPARCEL ON LANDOWNER.OWNER_ID = LANDPARCEL.OWNER_ID INNER JOIN LANDUSAGE ON LANDPARCEL.PARCEL_ID = LANDUSAGE.PARCEL_ID INNER JOIN CROP ON LANDUSAGE.CROP_ID = CROP.CROP_ID
WHERE CROP.CROP_NAME = 'WHEAT' AND CROP.CROP_SEASON = 'SPRING' AND LANDPARCEL.PARCEL_SIZE > 50
ORDER BY LANDPARCEL.PARCEL_SIZE DESC;
In addition, assume that the database statistics indicates the following:
The LANDOWNER table contains 10 records.
The LANDPARCEL table contains 10 records.
The CROP table has 10 different crops.
The LANDUSAGE table consists of 20 usage records (linking parcels to crops with usage dates).
There are 6 records of 'WHEAT' in the CROP table. 5 of those records represent 'WHEAT' grown in the 'SPRING' season.
There are 8 land parcels larger than 50 hectares.
'WHEAT' has been grown 6 times in total. Among these, 5 occurrences have been during the 'SPRING' season.
There are 2 landowners who have grown 'WHEAT' in the 'SPRING' season on parcels larger than 50 hectares.
Task 6: Creating Access Plans
a) Create two (2) alternative access plans for the given SQL query. Each plan should demonstrate a possible execution strategy for the query, along with an estimate of the corresponding I/O costs. The access plans must be presented in a structured tabular format using the following columns:
STEP: The sequence in which operations are performed during the execution of the query.
OPERATION: The specific database operation carried out at each step (e.g., selection, projection, cartesian product).
I/O OPERATIONS: The number of rows involved in the operation.
I/O COST: An estimate of the number of I/O disk reads required to complete the operation.
RESULTING SET ROWS: The number of rows output from the operation, which are used in subsequent steps.
TOTAL I/O COST: The cumulative I/O costs up to and including the current step.
You are only required to estimate the number of I/O disk reads in the I/O Operations and I/O Cost columns. Assume that no indexes exist and that each row read has an I/O cost of 1.
b) Select the access plan that provides the best performance for query execution. Provide a brief explanation justifying why this plan is the optimal choice.
Task 7: Optimising Queries Using Indexing
You are tasked with optimising the query performance through indexing.
a) Identify the columns that should be indexed and explain how each index will contribute to improving query performance.
b) Revise the optimal access plan from Task 6(b) to incorporate the identified indexes and recalculate the I/O costs based on these changes.
c) Provide a brief discussion on whether your approach with indexes optimised the execution of the query.
PART C - DATABASE ADMINISTRATION AND SECURITY (15 POINTS)
Overview
You are the Database Administrator (DBA) for the Lincoln Environmental Research Institute, an institute dedicated to environmental sustainability research. The institute manages a MySQL database to store essential data about researchers, projects, and funding details for various environmental studies.
Below is the SQL script for the key tables used in the database:
CREATE TABLE Researchers (
researcher_id INT AUTO_INCREMENT PRIMARY KEY, researcher_name VARCHAR(100),
division VARCHAR(50), clearance_level INT, salary DECIMAL(10, 2)
);
CREATE TABLE Projects (
project_id INT AUTO_INCREMENT PRIMARY KEY, title VARCHAR(200),
division VARCHAR(50), budget DECIMAL(12, 2), is_sensitive BOOLEAN, researcher_id INT,
FOREIGN KEY (researcher_id) REFERENCES Researchers(researcher_id)
);
CREATE TABLE Funding (
funding_id INT AUTO_INCREMENT PRIMARY KEY,
project_id INT, funding_amount DECIMAL(12, 2), funding_source VARCHAR(100), funding_date DATE,
FOREIGN KEY (project_id) REFERENCES Projects(project_id)
);
As the DBA, you are responsible for creating database objects and managing access control to them, ensuring that appropriate privileges are granted to users while maintaining security and data integrity.
Task 8: Managing Access Control
a) Write SQL statements to define the following views:
1. ResearcherNames: This view should display only the researcher_name from the Researchers table.
2. DivisionBudgets: This view should display each division, along with the average budget (avg_budget) and the total number of projects (project_count) using data from the Projects table.
3. SensitiveProjects: This view should include project_id, title, division, and budget for all projects where is_sensitive is set to TRUE.
4. HighValueFundingProjects: This view should display funding_id, project_id, funding_amount, funding_source, and funding_date for projects from the Funding table with a funding_amount greater than 1,000,000.
b) Alex (username: finance_user) is a member of the finance team and needs access to division-level budget summaries. Write the SQL statement to grant Alex read-only access to the DivisionBudgets view, which provides information about the average budget and total number of projects for each division.
c) If Alex's role is later expanded to include responsibility for managing funding details related to high-value projects, write the SQL statement needed to grant Alex the appropriate privileges to both view and modify records in the HighValueFundingProjects view.
d) As the DBA, describe the necessary steps you would take to ensure Alex's privileges are configured correctly.
e) Dina (username: dina_admin) is your assistant in charge of HR-related responsibilities. Write the SQL statements needed to grant her the ability to read, modify, and delete records in the Researchers table so she can manage researcher data effectively.
f) Dina is also responsible for managing the visibility of public researcher information, write the SQL statement that gives her the ability to grant read access on the ResearcherNames view to other users as needed.
g) Later, Dina grants access to the ResearcherNames view to Eli (username: eli_researcher). After Dina resigns from her role, you revoke all her database privileges. Discuss what impact this revocation has on Eli's access to the ResearcherNames view.
h) As you prepare to take a six-month sabbatical, you want Kai (username: kai_senior), your senior deputy, to have full administrative control over the Researchers, Projects, and Funding tables. Write SQL statements to grant Kai complete control (including the ability to delegate these privileges) over these tables.
i) While you are away, Kai grants read-only access to the Projects table to Maya (username: maya_temp), a temporary staff member. Upon your return, you decide to revoke Maya's access while preserving Kai's rights. Can this be done in MySQL? If so, write the appropriate REVOKE statement. If not, provide a clear explanation of the limitation and its implications.
j) During your absence, Kai also creates a view named SensitiveResearchSummary based on the SensitiveProjects view. Kai grants read-only access to Maya (maya_temp), who then extends access to Leo (leo_contractor), a contractor working temporarily. You now decide that both Maya and Leo should no longer have access to this view. Write SQL statements to revoke their access entirely. Explain what impact, if any, this revocation has on Kai's own privileges on the underlying SensitiveProjects view. Discuss whether the SensitiveProjects view will remain in the database after Maya and Leo lose access.
Hire our database experts to get help in your online coursework or projects. We have expertise in advance database design projects.
To get instant help you can contact us or send your project requirement details at:


Comments